Ensuring Online Data Safety: Best Practices for a Secure Digital Life
In today's digital world, online data safety has become a pressing concern for individuals and organizations alike. With the rise of cyber threats and data breaches, it's essential to adopt robust best practices to safeguard valuable data. This article will delve into the world of online data safety, exploring the top best practices to mitigate risks, prevent breaches, and secure sensitive information.Classify Data by Sensitivity: A Key Online Data Safety Best Practice
One of the most critical online data safety best practices is to classify data by sensitivity. This involves categorizing data into three levels of sensitivity: public, private, and confidential. Public data includes general information that can be shared with anyone, while private data includes sensitive information that requires protection, such as financial information or personal details. Confidential data includes highly sensitive information that requires strict protection, such as intellectual property or national security. By classifying data by sensitivity, organizations and individuals can implement targeted security measures to safeguard sensitive information, reducing the risk of data breaches and cyber attacks.Enforce Least Privilege: A Critical Online Data Safety Best Practice

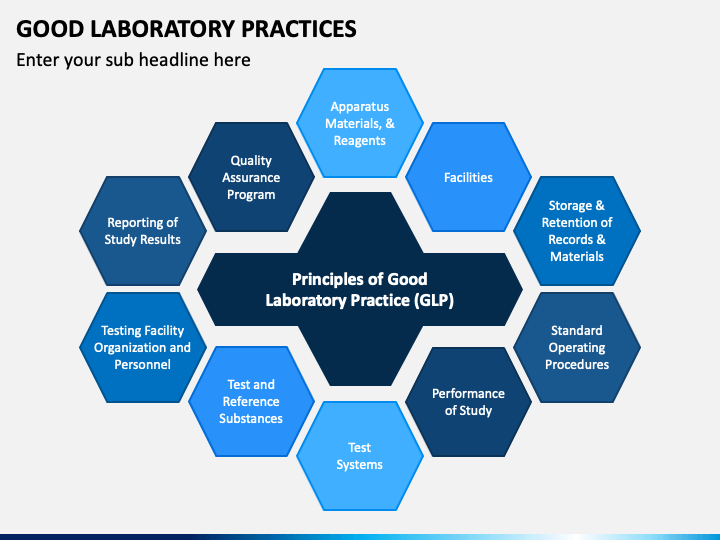
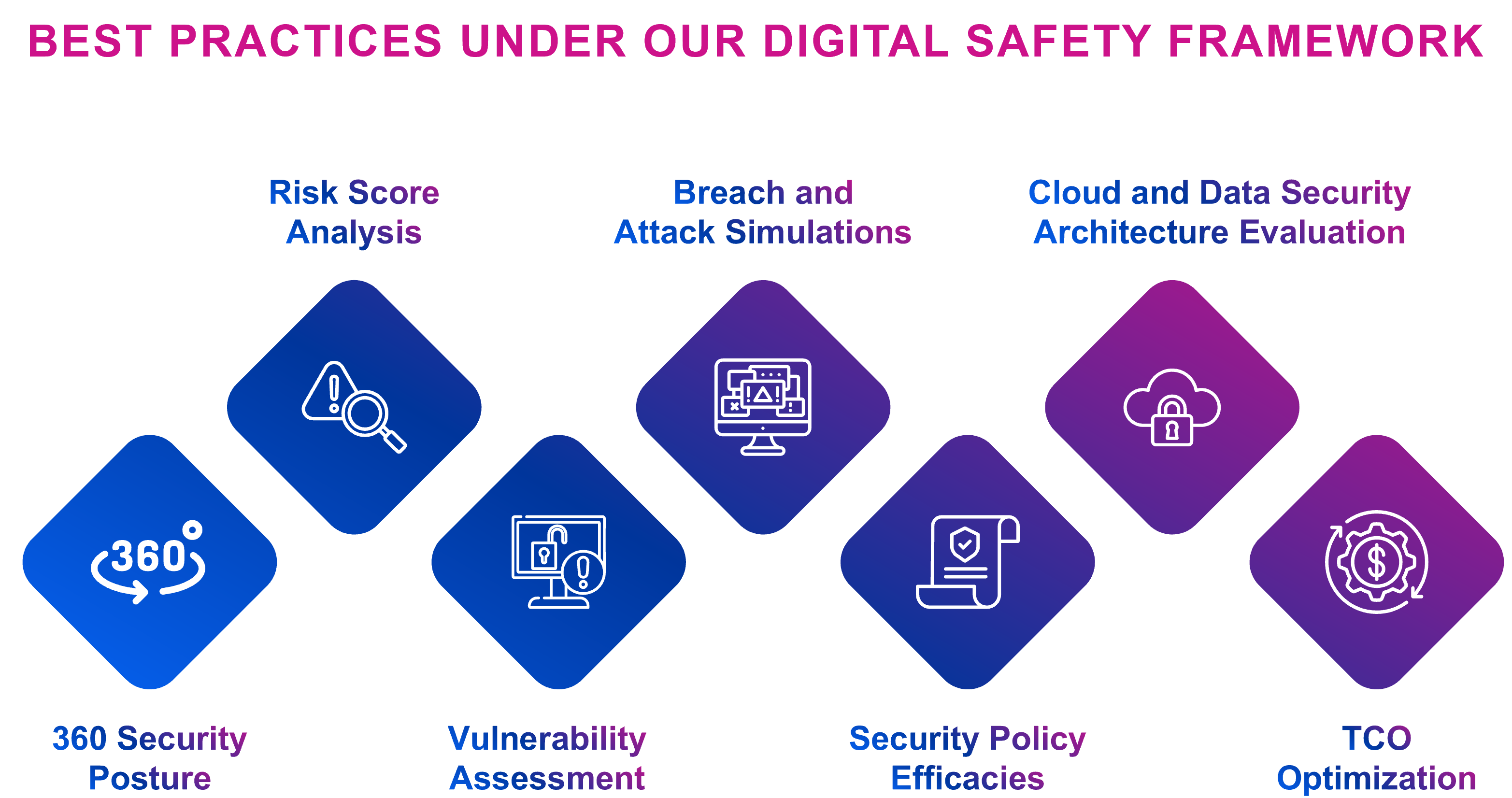
Furthermore, visual representations like the one above help us fully grasp the concept of Online Data Safety Best Practices.
Enforcing least privilege is another crucial online data safety best practice. This involves granting users the minimum level of access required to perform their job functions, reducing the risk of unauthorized access to sensitive data. By limiting user privileges, organizations can prevent data breaches caused by insider threats or misconfigured systems. To enforce least privilege, organizations can implement role-based access control (RBAC), which assigns users specific roles based on their job functions, rather than granting them blanket access to sensitive data.Secure Data at Rest: A Foundational Online Data Safety Best Practice
Securing data at rest is a foundational online data safety best practice that involves protecting data stored on servers, disks, and other storage devices. This includes implementing encryption, which scrambles data to prevent unauthorized access, as well as using secure protocols for data transmission. To secure data at rest, organizations can implement full disk encryption, which encrypts entire disks, including metadata and system files. This provides an additional layer of protection against data breaches and cyber attacks. Detecting misuse is a proactive online data safety best practice that involves monitoring user activity to identify and respond to potential security threats. This can include implementing intrusion detection systems (IDS), which analyze network traffic for signs of malicious activity, as well as monitoring user activity for suspicious behavior. To detect misuse, organizations can implement behavioral analytics, which analyze user behavior to identify patterns that may indicate insider threats or malicious activity.Best Practices for Securing Data in Transit

Implement Regular Backups: A Critical Online Data Safety Best Practice
Implementing regular backups is a critical online data safety best practice that involves creating and storing copies of data to ensure its availability in the event of a data loss or breach. This includes implementing automated backups, which can be performed daily, weekly, or monthly, depending on the organization's needs. To implement regular backups, organizations can use cloud-based backup services, which provide secure, on-demand access to backups, as well as automated backup scheduling and retention policies.Stay Up-to-Date with the Latest Threat Intelligence: A Critical Online Data Safety Best Practice

Conduct Regular Security Audits: A Critical Online Data Safety Best Practice
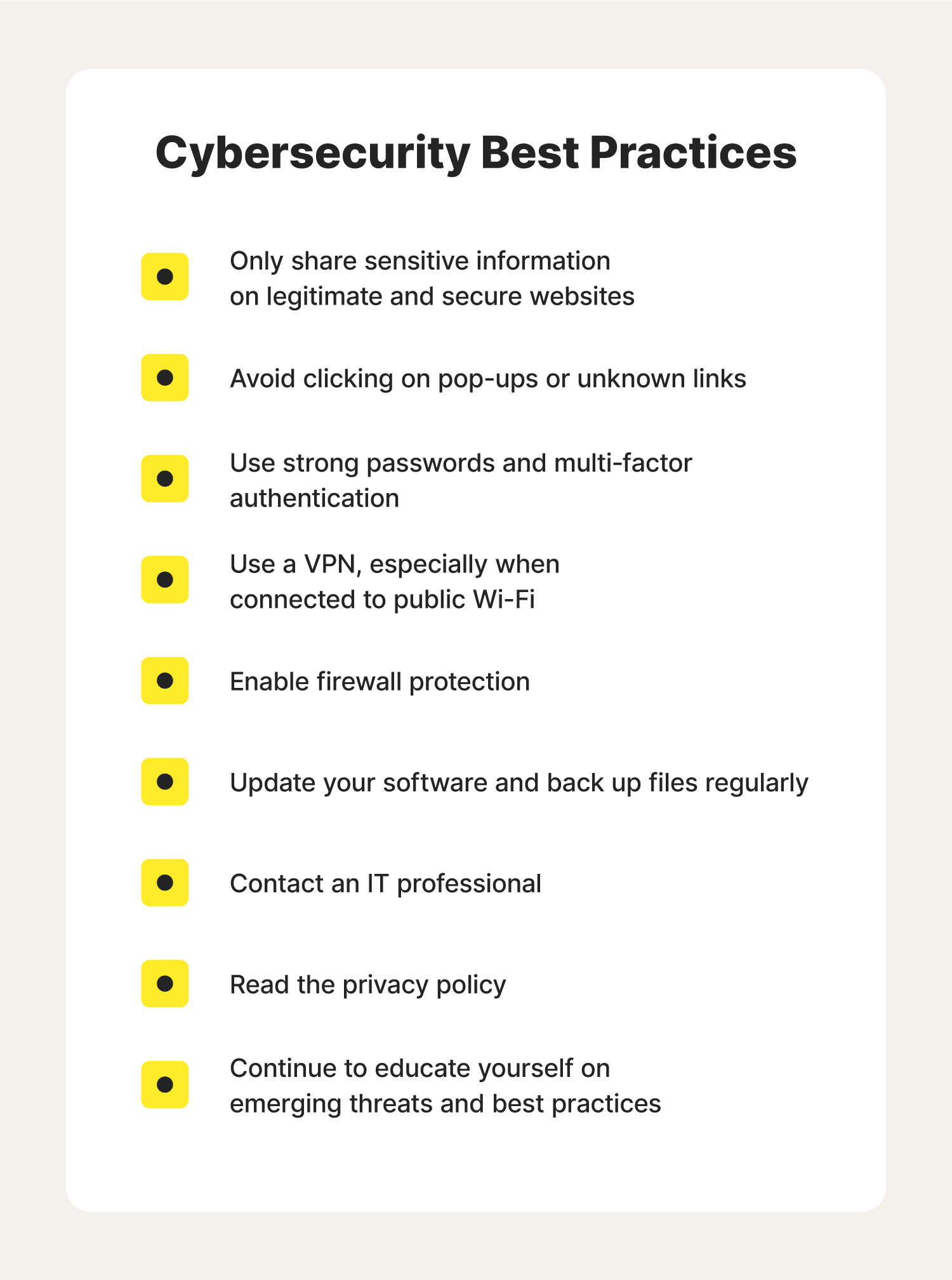
Conducting regular security audits is a critical online data safety best practice that involves periodically assessing and evaluating an organization's security controls to identify vulnerabilities and take corrective action. This includes conducting vulnerability scanning, penetration testing, and security assessments to identify potential security weaknesses. To conduct regular security audits, organizations can engage with external auditors or security consultants to conduct security assessments and provide recommendations for improvement. Raising awareness and educating users is a foundational online data safety best practice that involves educating users about online data safety and the importance of following security best practices to prevent data breaches and cyber attacks. To raise awareness and educate users, organizations can develop and implement training programs, which can include security awareness training, phishing simulation, and password management training. By implementing these online data safety best practices, organizations and individuals can reduce the risk of data breaches and cyber attacks, while ensuring the security and integrity of sensitive data. By staying informed and up-to-date with the latest threat intelligence and security best practices, organizations and individuals can stay ahead of emerging threats and ensure a secure digital life.- Classify data by sensitivity
- Enforce least privilege
- Secure data at rest
- Secure data in transit
- Detect misuse
- Implement regular backups
- Stay up-to-date with the latest threat intelligence
- Conduct regular security audits
- Raise awareness and educate users












![Python Exercises, Practice, Challenges [385+ Exercises] - PYnative Python Exercises, Practice, Challenges [385+ Exercises] - PYnative - Online Data Safety Best Practices](https://static.vecteezy.com/system/resources/previews/046/452/129/non_2x/data-privacy-set-cyber-or-web-security-database-safety-of-a-digital-device-vector.jpg)








-A4.jpg)
