##
How to Secure WiFi Network with Incident Response Plan
In today's digital age, the security of wireless networks is a top priority for organizations of all sizes. A properly secured WiFi network is crucial to protect sensitive data from unauthorized access. However, with the increasing complexity of cyber threats, even the best-laid plans can go awry. This is where an Incident Response Plan comes into play, providing your organization with a comprehensive strategy to detect, respond to, and recover from security incidents. ##Understanding the Risks of Unsecured Wireless Networks

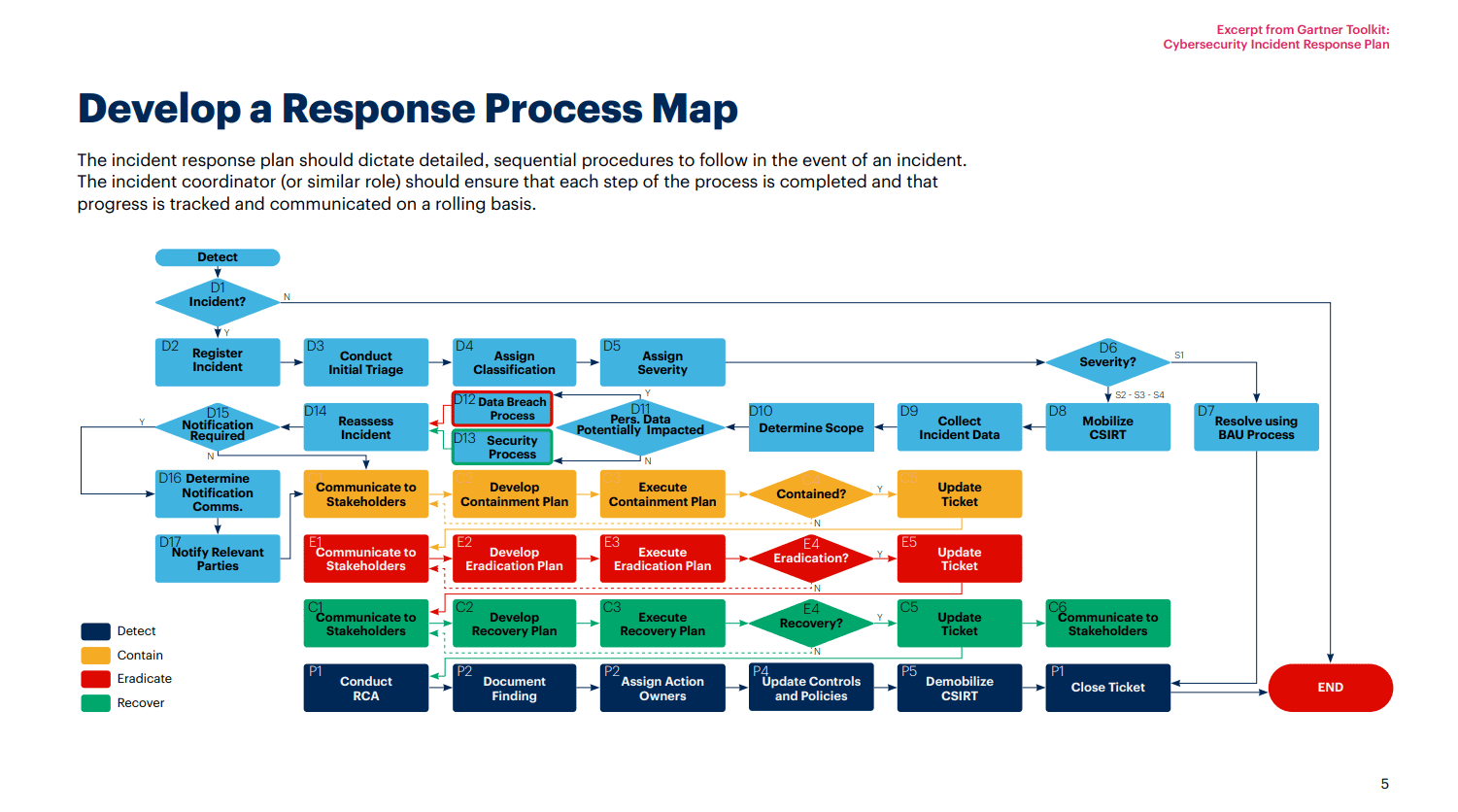
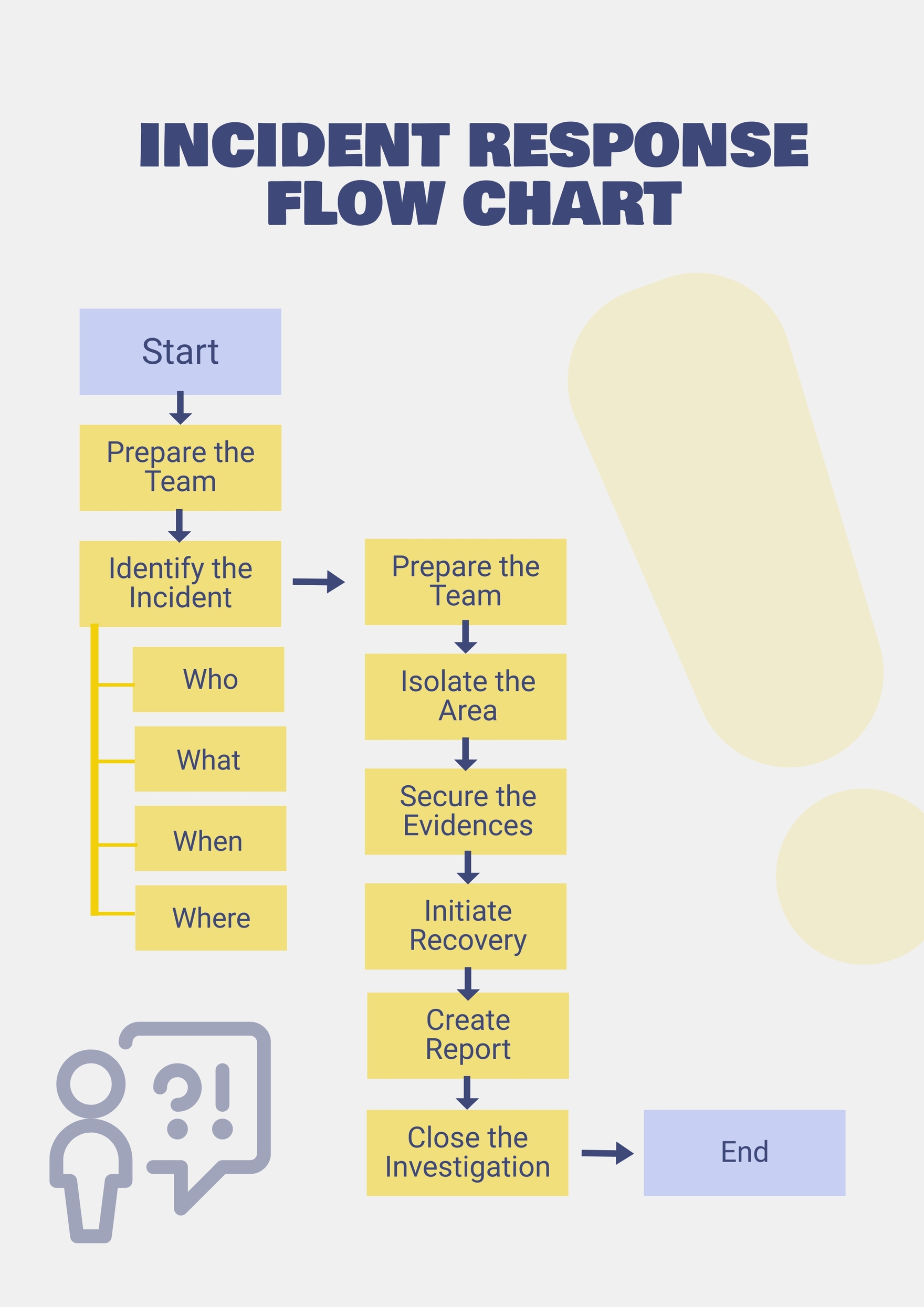
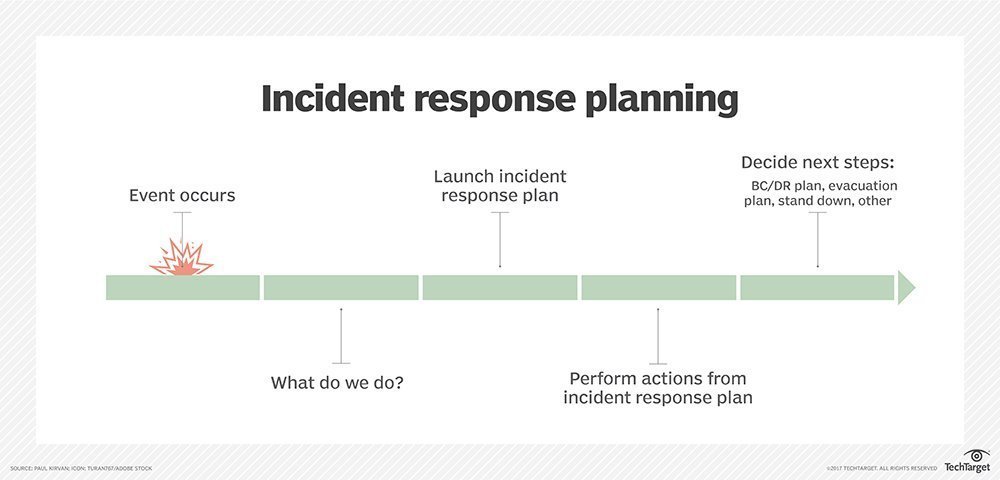
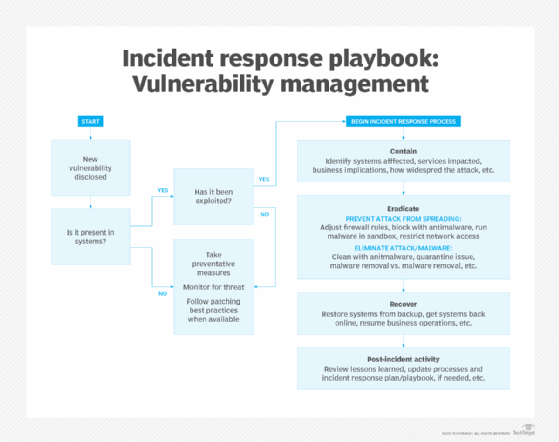
Furthermore, visual representations like the one above help us fully grasp the concept of How To Secure Wifi Network With Incident Response Plan.
An unsecured wireless network is like an open invitation to cyber attackers. Without proper security measures in place, your network is vulnerable to: * Malware attacks * Data breaches * Unauthorized access * Denial of Service (DoS) attacks ##Creating an Effective Incident Response Plan
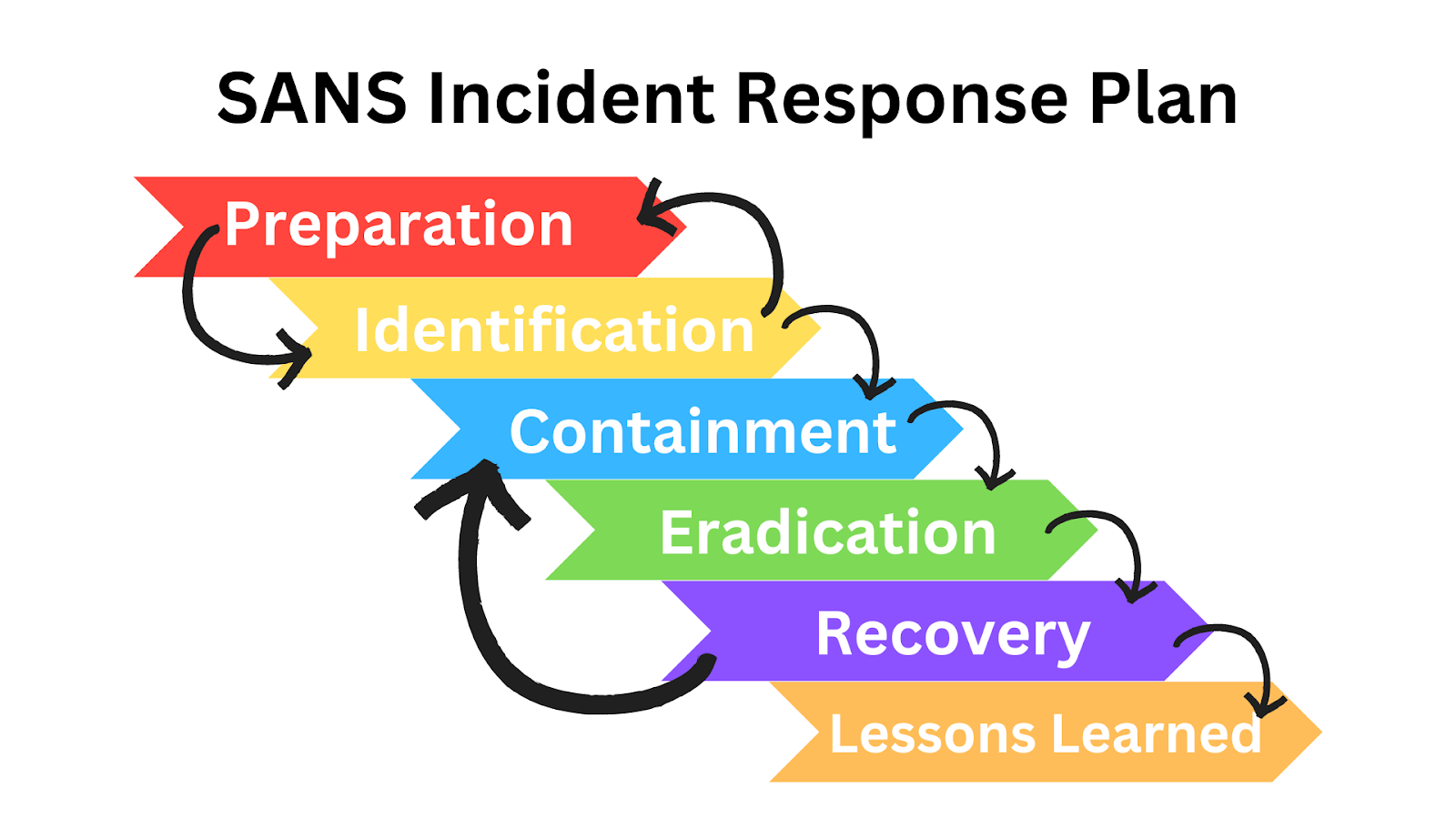
A well-crafted Incident Response Plan is the key to mitigating the effects of a security incident on your organization. Here are some key steps to create a comprehensive plan: ###Step 1: Preparation

Such details provide a deeper understanding and appreciation for How To Secure Wifi Network With Incident Response Plan.
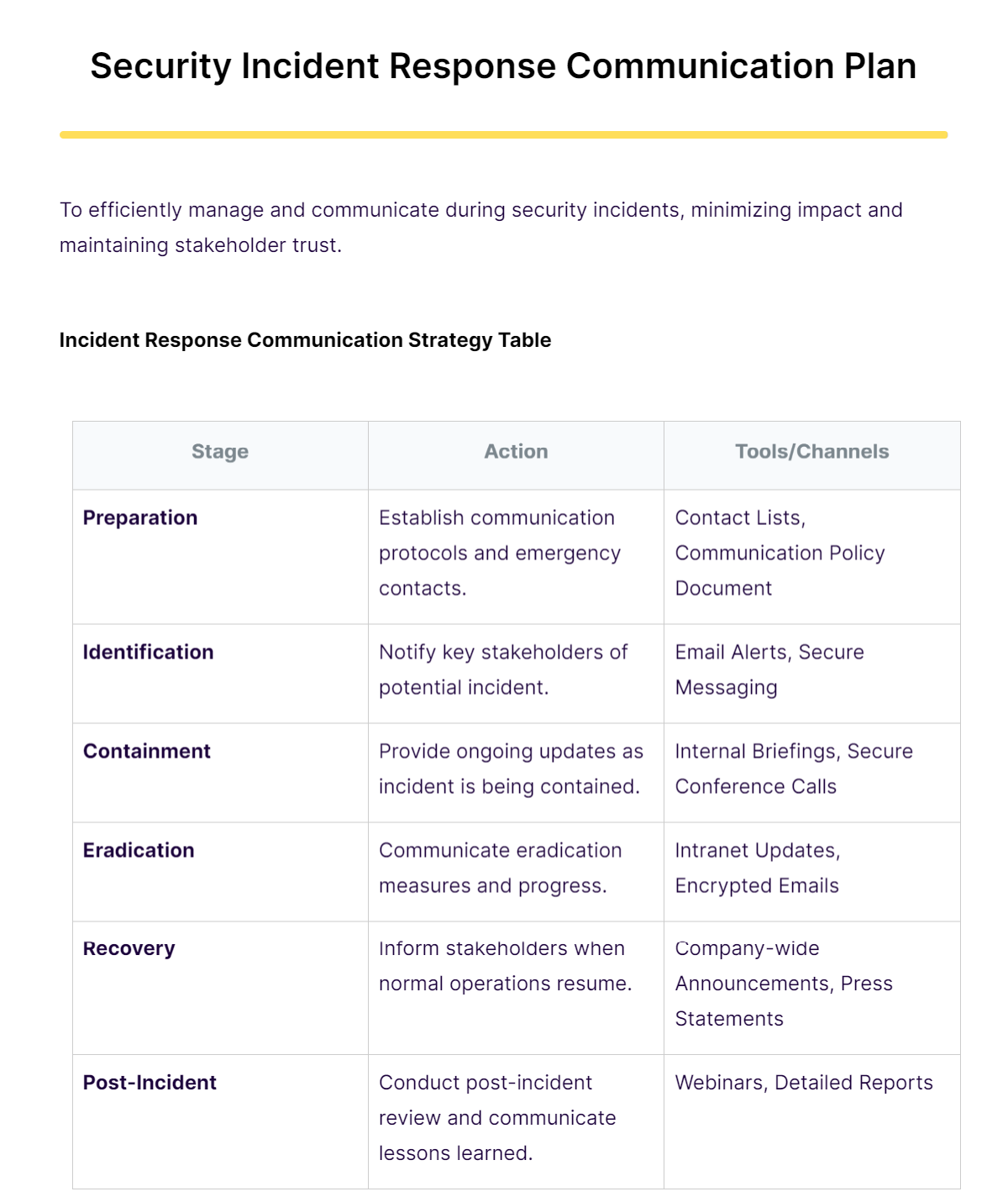
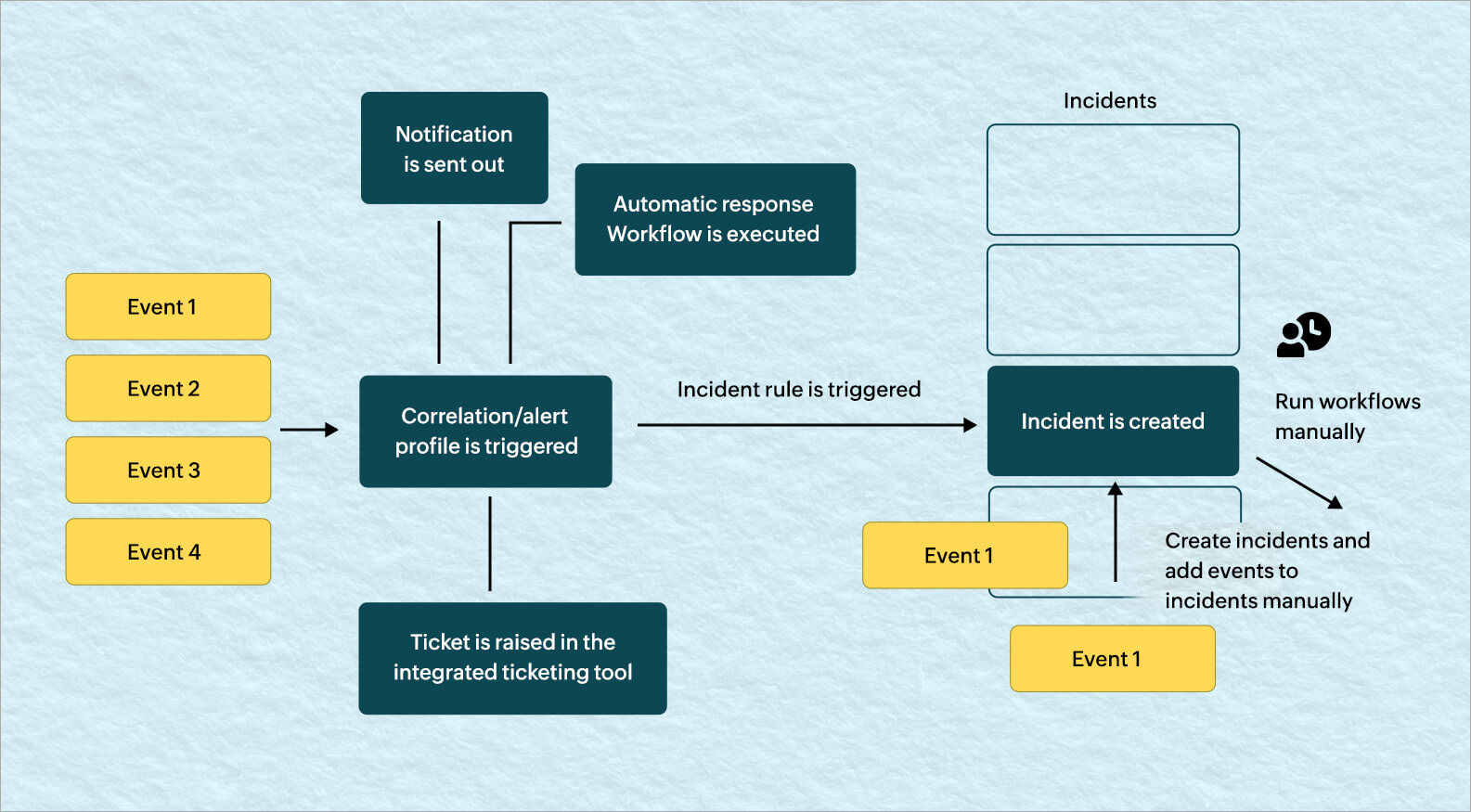
* Define your Crisis Management Team (CMT) and assign roles and responsibilities. * Identify potential security threats and risks to your organization. * Develop a list of emergency contacts and communication protocols. ### * Establish a system for identifying and reporting security incidents. * Develop a procedure for containing and mitigating the effects of a security incident. * Establish a protocol for communicating with stakeholders and managing media relations. ###













![What Is Incident Response? Process, Practices & Automation [2025] - Cynet Picture of What Is Incident Response? Process, Practices & Automation [2025] - Cynet](https://cybersecuritymasters.in/wp-content/uploads/2023/05/Whatisincidentresponseincybersecurity.png)