Preventing Malware from Spreading in Network: A Comprehensive Guide
Understanding the Threat of Malware
Malware is one of the biggest threats to the security of your computer, tablet, phone, and other devices. It can spread quickly and cause significant damage, compromising sensitive information and disrupting business operations. In this article, we'll explore the different types of malware, how they spread, and most importantly, provide you with actionable tips on how to prevent malware from infecting your network.
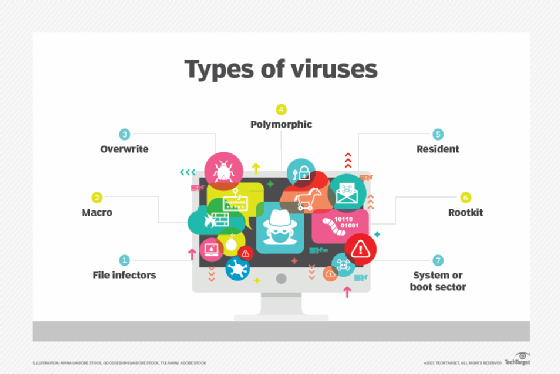
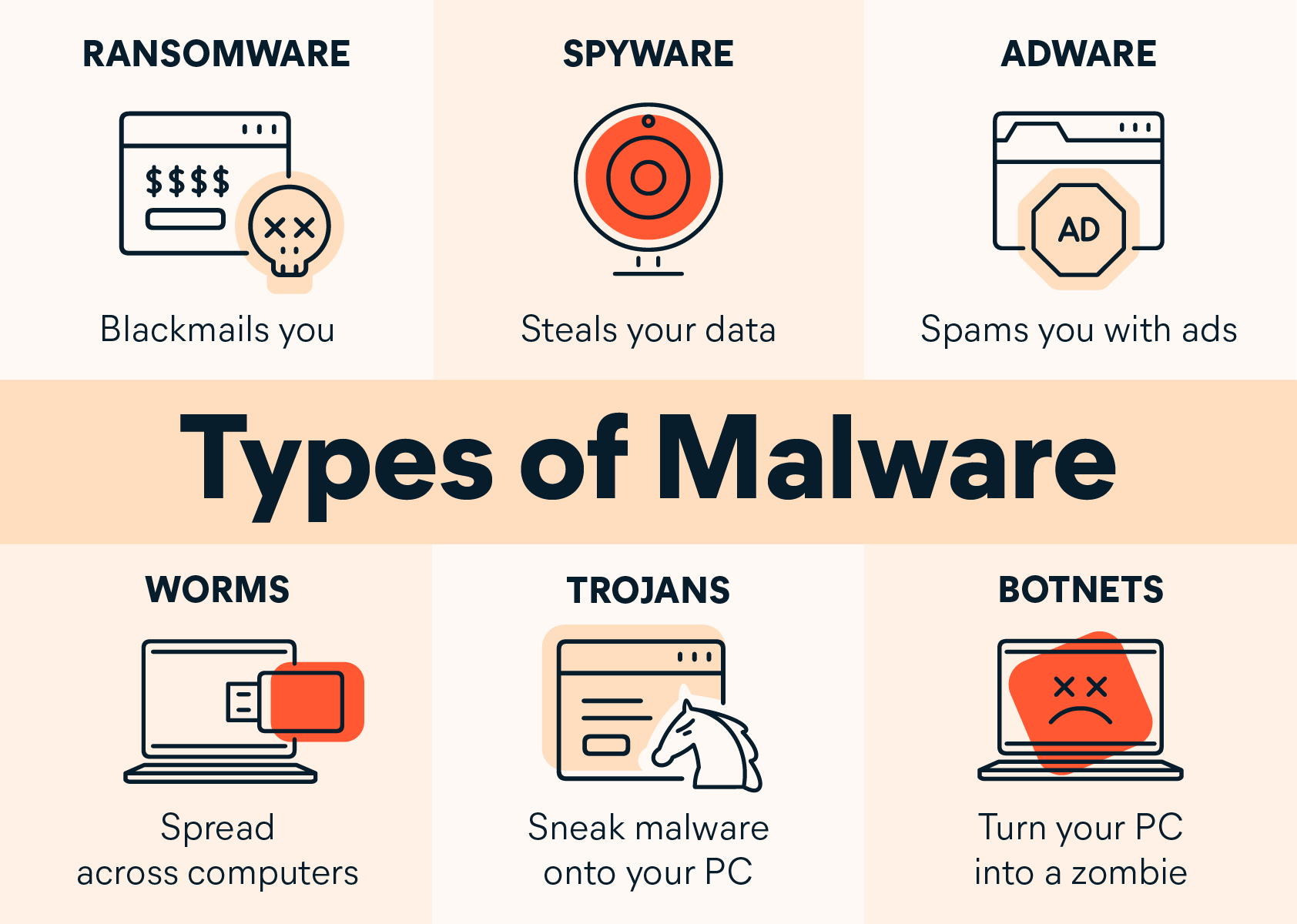
Types of Malware and their Transmission Methods
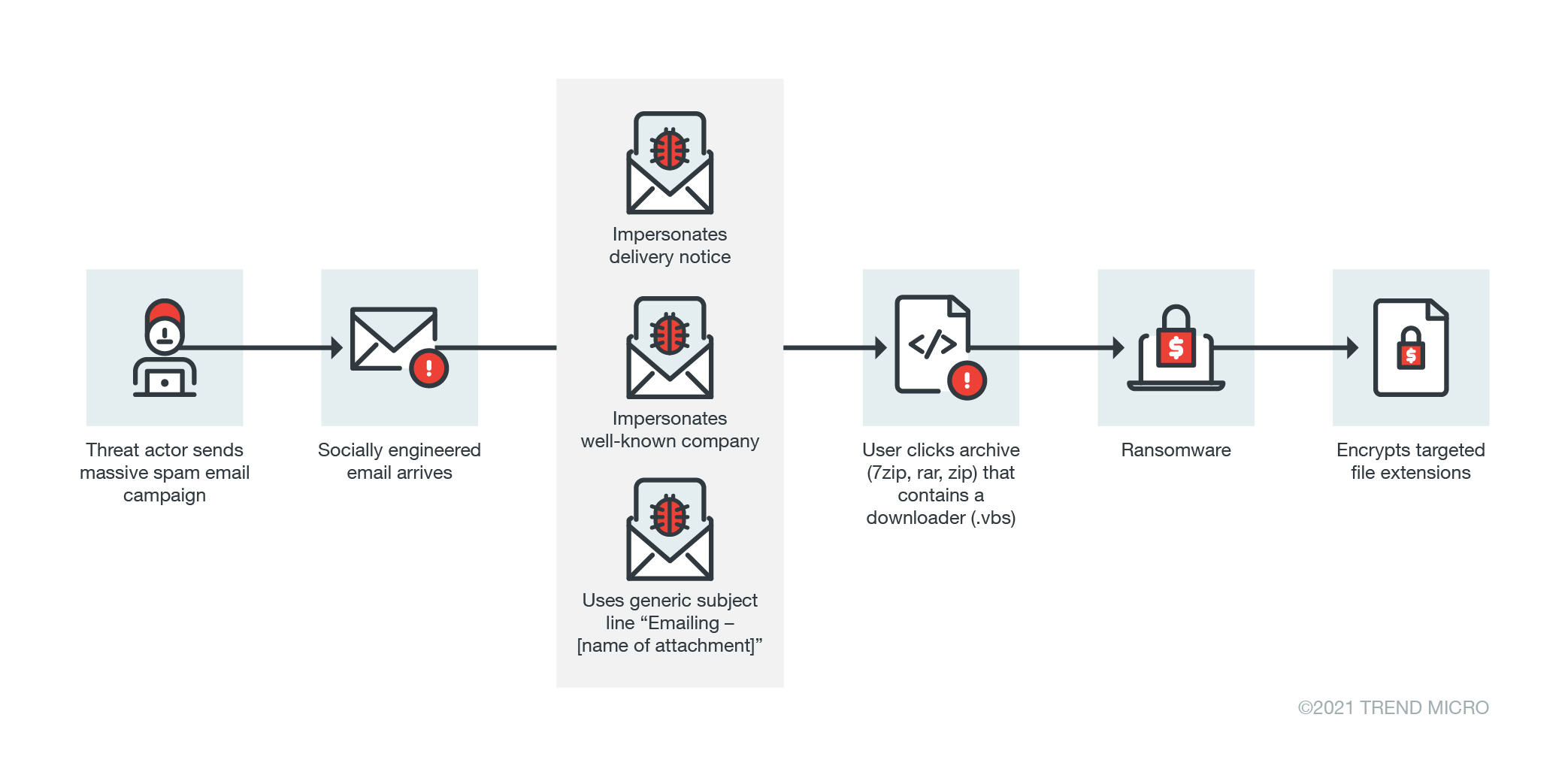
There are various types of malware, including adware, spyware, viruses, worms, Trojans, ransomware, rootkits, keyloggers, cryptominers, and exploits. Malware spreads mainly through hacked sites, malicious downloads, risky apps, and phishing emails. It's essential to be aware of the common infection signs, such as slow performance, pop-ups, crashes, strange network activity, or changed settings.
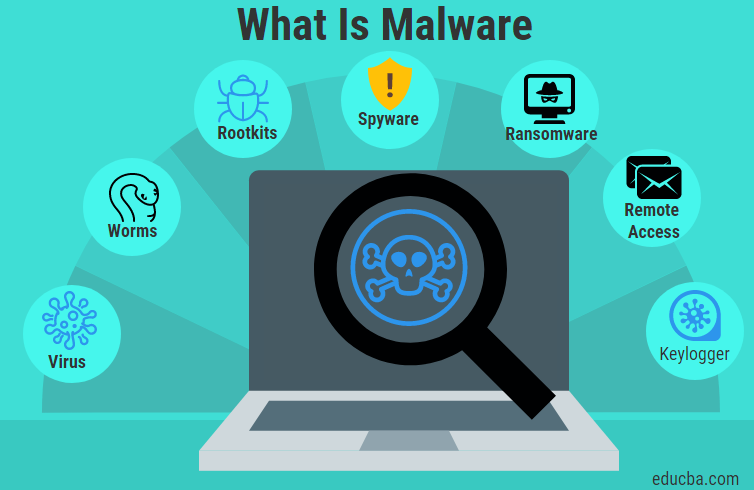
Moving forward, it's essential to keep these visual contexts in mind when discussing Preventing Malware From Spreading In Network.
Malware Lateral Movement: A Growing Concern
Malware lateral movement is a technique attackers use to spread from one compromised system to others within the same network. This allows them to expand their control and reach deeper into an organization's infrastructure, often undetected for extended periods.
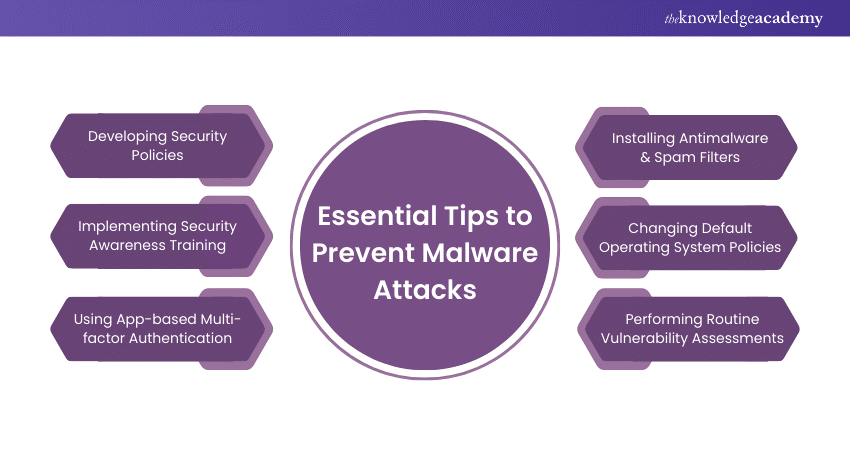
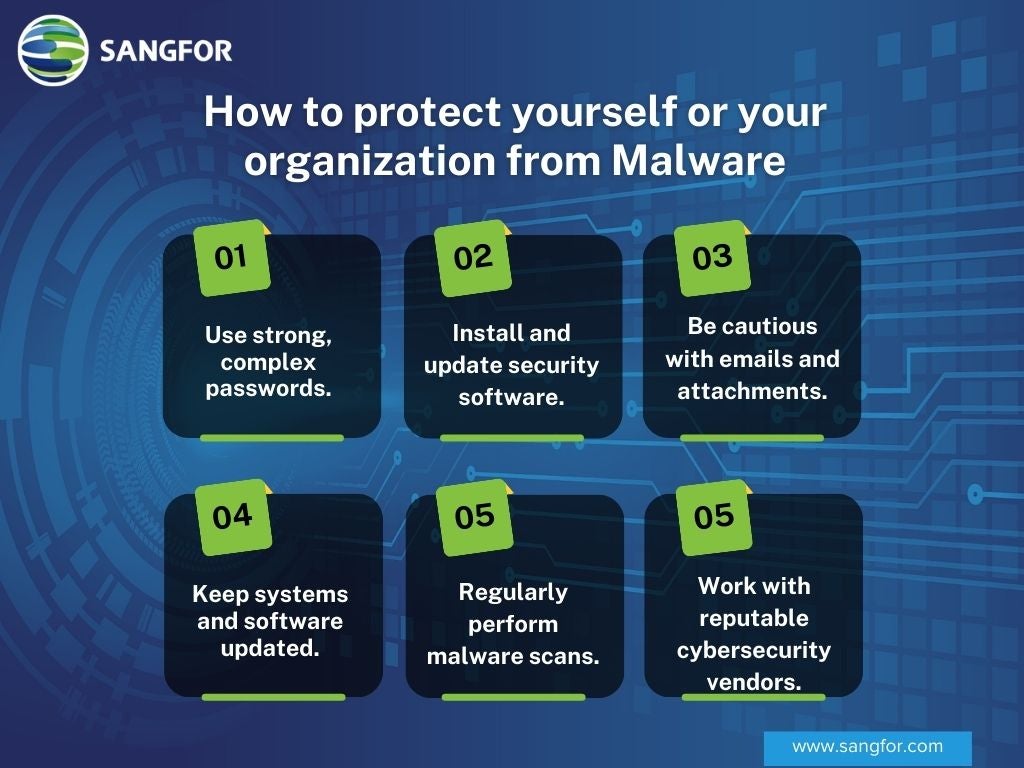
Preventing Malware from Spreading: Best Practices
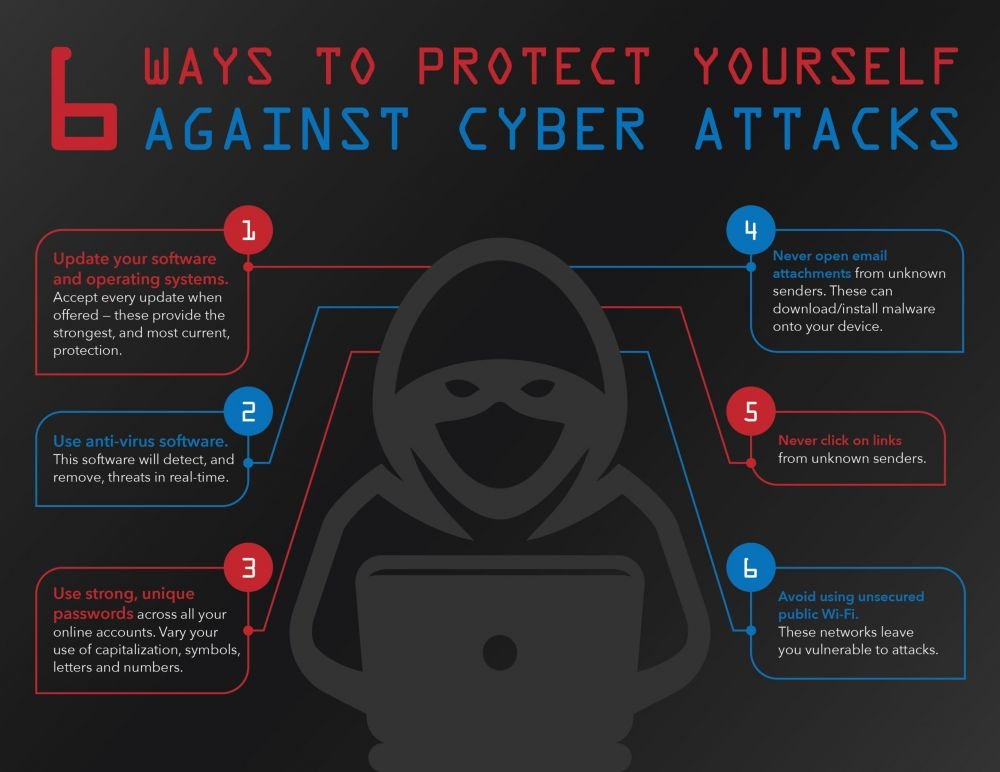
Preventing malware from spreading in a network requires a combination of technical measures and employee education. Here are some best practices to prevent malware from infecting your network:

- Keep Your Software Up-to-Date:** Regularly update your operating systems, applications, and firmware to prevent known vulnerabilities.
- Use Strong Passwords:** Implement a password policy that requires strong, unique passwords for all users and administrators.
- Install Anti-Malware Software:** Use reputable anti-malware software that can detect and remove malware threats.
- Use Network Segmentation:** Divide your network into different subnets with different security policies and controls to limit lateral movement.
- Implement Network Monitoring:** Regularly monitor your network for suspicious activity using intrusion detection systems and network traffic analysis tools.
- Use Encryption:** Encrypt sensitive data both in transit and at rest to prevent unauthorized access.
- Conduct Regular Security Audits:** Perform regular security audits to identify vulnerabilities and ensure that your security controls are effective.
Isolating Infected Systems: A Critical Step
Once malware is detected on a device, isolate it from the network immediately to prevent further spread. This includes disconnecting it physically or logically, disabling wireless connections, and turning off Bluetooth or any other communication channels.